Cloud-based services top 10 technologies for 2012 – StartupSmart
Cloud-based solutions and virtualisation are among the top technologies tipped to take off in 2012, according to Quest Software, amid increasing demand for mobility and collaboration.
Quest Software recently compiled a list of 10 predictions for technology in 2012, with an emphasis on software-as-a-service, cloud computing, virtualisation, and mobile technologies.
Ian Hodge, Quest Software managing director for Australia and New Zealand, says these technologies are reshaping how and where applications are managed and delivered.
“The implications on communications, security, provisioning and systems management are enormous. How organisations are addressing these opportunities [is important],” he says.
Hodge outlines the top 10 technologies for 2012 as identified by Quest Software:
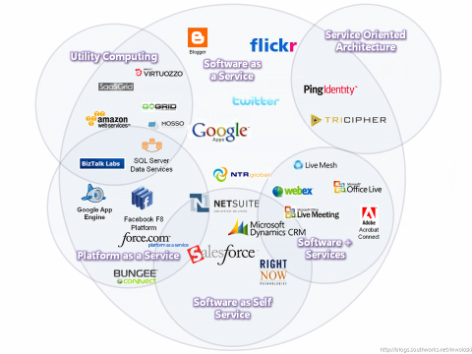
1. SaaS growth will help drive wider adoption of cloud services.
SaaS offerings cover a broad spectrum of business and technical applications.
However, shared business services – such as messaging, customer relationship management and human resources – have emerged as the most popular solutions.
2. Cloud service providers must overcome key concerns to accelerate acceptance.
According to Quest, public cloud services raise concerns over compliance, security and access management controls.
These concerns must be recognised and allayed through better tools and practices, improved auditability and solution certification.
3. Microsoft Hyper-V will make inroads in overcoming VMware’s market dominance.
While VMware is viewed as more robust and feature-rich than Microsoft Hyper-V, more organisations are willing to pilot and deploy Hyper-V due to its improving features and incorporation within Server 2008 R2.
4. Ongoing issues will create opportunities for “virtualisation-aware” solutions.
Quest believes backup, performance monitoring and storage monitoring remain problematic for most organisations.
However, backup concerns should lessen in the future as niche providers start to offer special-purpose backup tools for virtualisation.
5. Cloud workloads will remain largely isolated for the foreseeable future.
Due to concerns about security, control and technology maturity, most organisations isolate internal and external workloads.
As a result, cloud-bursting – which is the practice of moving excess workloads to an external cloud on an on-demand basis – has yet to gain any traction among IT companies.
6. Google and Microsoft will challenge Apple’s lead in the IT mobile market.
When deciding which platforms to support, companies must balance current market share and capabilities against long-term potential.
While Apple iOS is currently in the lead, the strong performance of Google Android is a reflection of where the market will head as its sales increase and capabilities improve.
Meanwhile, Microsoft remains a strong contender with Windows 7.
7. Cloud applications, compliance and mobile devices will reshape corporate identity and access management (AIM) strategies.
New compliance mandates, the growth of cloud-based applications and the uptake of mobiles devices are causing companies to rethink their user provisioning strategies to control support costs and better manage security.
8. Active Directory will continue to dominate and the IAM framework will see modest growth.
According to Quest, Active Directory is the preferred identity management platform for businesses. Meanwhile, modest growth is expected in both the Microsoft and non-Microsoft framework categories.
9. Office 365 will see slow adoption, except among small businesses.
Cloud-based email solutions offer organisations an alternative for outsourcing their corporate email systems.
Although on-premise systems (namely Microsoft Exchange) still dominate, cloud-based email solutions are catching on with early adopters.
Quest predicts Microsoft will find traction for Office 365 among small businesses, and this is where most of Microsoft’s growth will come from.
10. Employers will face increased monitoring of their social networking activities.
According to Quest, most organisations are “running blind” without any visibility into the breadth and depth of social networking use among their staff.
Over time, reporting solutions will be implemented and tougher controls will emerge.